Mon-Fri, 9:00-17:00 (Beijing Time, UTC+8)
Mon-Fri, 9:00-17:00 (Beijing Time, UTC+8)Risk Control and Compliance Assurance
Real-time payment risk control intercepts abnormal transactions; a global compliance engine adapts to regulations in multiple countries; dual protection via permission isolation and data anonymization prevents privacy breaches and legal risks.
Core Advantages

Payment Risk Control
Real-time monitoring of anomalous transactions, with automatic interception via integration with international payment gateways.

Global Compliance Engine
Automatically adapts to target market regulations (e.g., EU GDPR, CCPA, product certifications) to avoid legal risks.

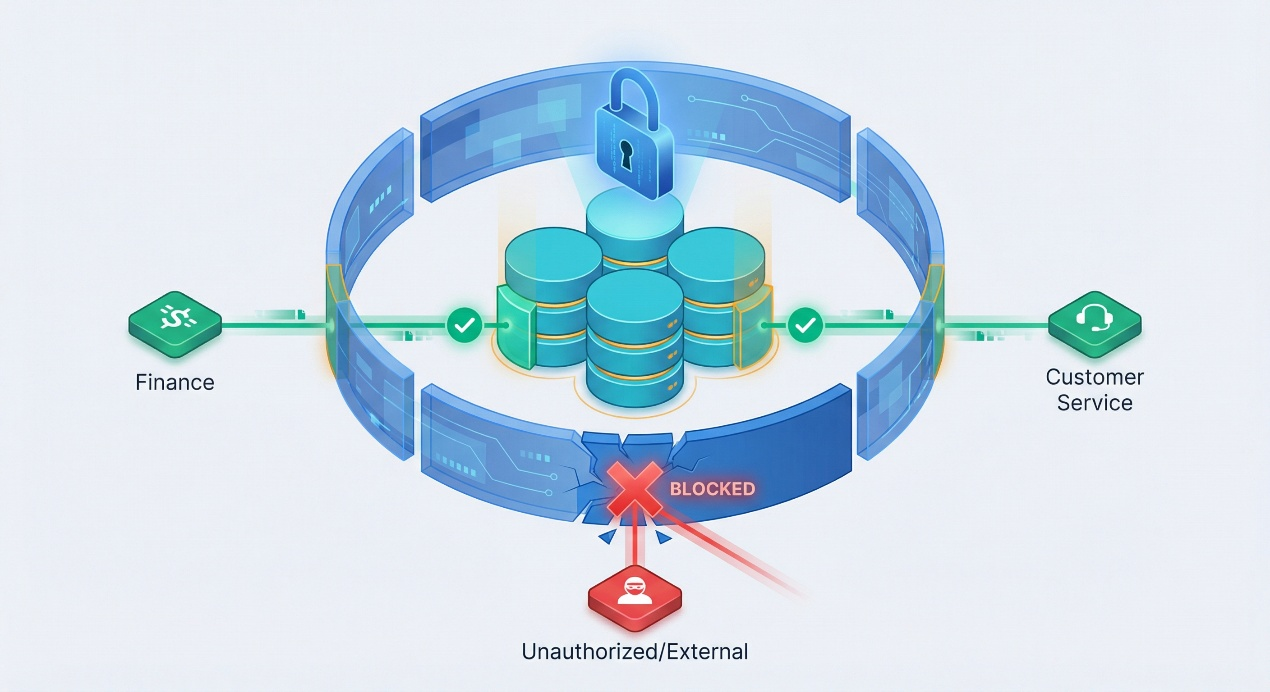
Data Security and Permission Isolation
Sensitive operations require multi-factor verification; supports role-based data access permissions (e.g., customer service agents can view only order logistics information).

Customer Privacy Protection and Data Anonymization
Automatically identifies and anonymizes users' sensitive information (e.g., phone numbers, ID numbers), restricts access to and dissemination of sensitive data, and eliminates risks of privacy breaches and regulatory violations.
Risk Control and Compliance Assurance: Building a Secure and Trustworthy Operational Foundation for Global E-commerce
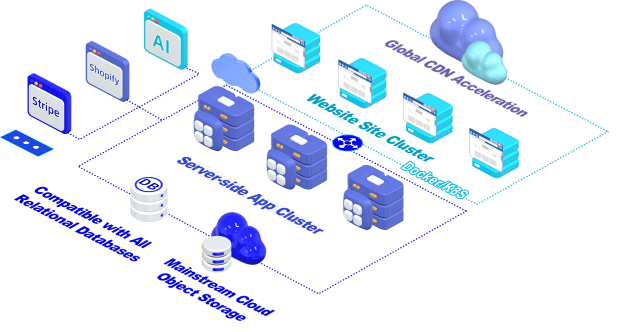
Introduction: Amid the dual waves of e-commerce globalization and increasingly stringent regulatory oversight, risk control is no longer a "optional feature" for enterprises—it is a "must-answer question" for survival and growth. A single payment vulnerability may lead to losses amounting to millions; a single data breach may trigger class-action lawsuits and exorbitant regulatory fines; a single compliance failure may result in immediate expulsion from core markets. BMS Digital Experience Platform e-commerce engine module delivers robust risk control and compliance support to platforms through multi-layered security safeguards, compliance adaptation, and intelligent monitoring technologies. This article will delve into the platform’s core advantages, helping e-commerce businesses operate efficiently within compliance frameworks.
I. Payment Risk Control: Real-Time Anomaly Interception to Safeguard Financial Security
The payment process is the most sensitive segment of any e-commerce platform—and also the most vulnerable to risk. Through its payment risk control functionality,BMS Digital Experience Platform e-commerce engine module monitors every transaction in real time, automatically identifying potential fraudulent activities and anomalous transactions. By integrating with international payment gateways, the system can instantly perform intelligent interception upon detecting anomalies, preventing fraudulent transactions and financial loss.
Core Advantages:
Real-time Monitoring: The platform monitors anomalies during transactions in real time, preventing fraudulent activity.
Intelligent Interception: The automated system rapidly responds to and intercepts suspicious transactions, minimizing manual intervention.
Global Payment Security: Seamless integration with international payment gateways ensures the security of cross-border payments.
Through payment risk control technology, e-commerce platforms can reduce losses arising from payment-related risks, enhance transaction security, and strengthen consumer trust.
II. Global Compliance Engine: Automated Regulatory Adaptation to Mitigate Legal Risks
As e-commerce operations expand globally, regulatory requirements across jurisdictions are becoming increasingly diverse. For instance, the EU’s GDPR (General Data Protection Regulation) and the U.S.’s CCPA (California Consumer Privacy Act) mandate strict adherence to data protection, privacy, and consumer rights safeguards. Our Global Compliance Engine automatically adjusts the platform’s compliance strategy according to the legal requirements of each target market, helping enterprises avoid legal exposure.
Core Advantages:
Automated Regulatory Adaptation: The system dynamically adapts the platform’s compliance strategy based on the legal requirements of the target market.
Global Data Protection Compliance: Ensures platform adherence to global regulations such as GDPR and CCPA, avoiding legal risks stemming from noncompliance.
Product Certification & Compliance: Automatically verifies whether products meet target-market certification standards, ensuring smooth operations across countries.
The Global Compliance Engine provides e-commerce platforms with cross-border operational compliance assurance, effectively reducing legal risks inherent in cross-border e-commerce and ensuring compliant platform operations worldwide.
III. Data Security and Permission Isolation: End-to-End Protection from Entry to Exit
Data security is paramount for e-commerce platforms—especially amid escalating data breaches and cyberattacks. Effectively protecting user and enterprise data has become the top priority in platform operations. The Data Security and Permission Isolation module employs multi-factor authentication and stringent permission controls to ensure that sensitive operations and information access are restricted exclusively to authorized personnel.
Core Advantages:
Role-Based Permission Management: Granular data access permissions are assigned based on employee roles (e.g., customer service, operations, finance), preventing information misuse.
Principle of Least Privilege: Only employees requiring access to specific data are granted permissions, minimizing unnecessary data exposure and internal abuse.
Data security and permission isolation ensure internal data confidentiality and operational transparency, significantly reducing security risks arising from internal privilege misuse or external attacks.
IV. Customer Privacy Protection and Data De-identification: Intelligent De-identification Controls to Prevent Privacy Leaks
As consumer concern over privacy intensifies, e-commerce platforms must implement effective measures to safeguard users’ sensitive information. The Customer Privacy Protection and Data De-identification module automatically identifies and de-identifies customers’ sensitive data—for example, masking the middle four digits of phone numbers or the middle eight digits of ID numbers—ensuring uninterrupted business operations while effectively protecting user privacy. Simultaneously, it restricts access rights and dissemination scope for sensitive information, permitting only authorized personnel to view de-identified sensitive data—thereby eliminating leakage and unauthorized dissemination of sensitive information and strictly complying with global privacy regulations.
Core Advantages:
Automated Data De-identification: Applies de-identification to sensitive information to prevent user privacy leaks.
Access Control: Enforces strict access restrictions on sensitive information, ensuring visibility only to authorized personnel.
Privacy Protection Compliance: Meets global privacy regulations including GDPR and CCPA, safeguarding user data security.
Implementing this module not only effectively prevents data breaches but also enhances user trust in the platform and strengthens brand reputation.
Conclusion: Supported by these technological modules, e-commerce enterprises can focus on innovation and operational optimization while ensuring steady growth within secure and compliant frameworks. Whether operating domestically or internationally, the platform functions in a safer, more transparent, and fully compliant environment—delivering superior shopping experiences to users.
Frequently Asked Questions (FAQ)
Q1: How does payment risk control prevent payment fraud?
A1: Payment risk control analyzes various transaction data—including transaction amounts, payment methods, and user behavior—to detect anomalous patterns and identify risks in real time. Upon detecting suspicious transactions, the system automatically intercepts them, protecting both users and the platform from fraudulent activity.
Q2: How does the Global Compliance Engine help platforms adapt to regulations in different markets?
A2: The Global Compliance Engine automatically identifies target-market compliance requirements and dynamically adjusts the platform’s operational strategies. Whether concerning data protection, privacy compliance, or product certification, the Global Compliance Engine ensures continuous alignment with local regulations.
Q3: Can de-identified data still be used for analytics and operations?
A3: Yes—de-identified data remains fully usable for analytics and operations. Although sensitive information is masked, de-identified data supports behavioral analysis, user profiling, and market insights—enabling platforms to optimize operations and customer experience without violating privacy regulations.
Q4: Does the platform provide data access logs and audit functionality?
A4: Yes—the platform offers comprehensive data access logging and audit capabilities. All access to and operations on sensitive data are meticulously recorded. These logs assist platforms in tracking data access, identifying potential security vulnerabilities, and providing verifiable audit evidence when required—ensuring regulatory compliance.
Want to know more about our products?
With years serving Fortune 500 clients, we offer flexible solutions and integrated implementation.

Xiaohongshu

WeChat Channels

Douyin

Xiaohongshu

WeChat Channels

Douyin